Generating Certificates
See step-by-step instructions for generating certificates to be used for certificate based authentication here.
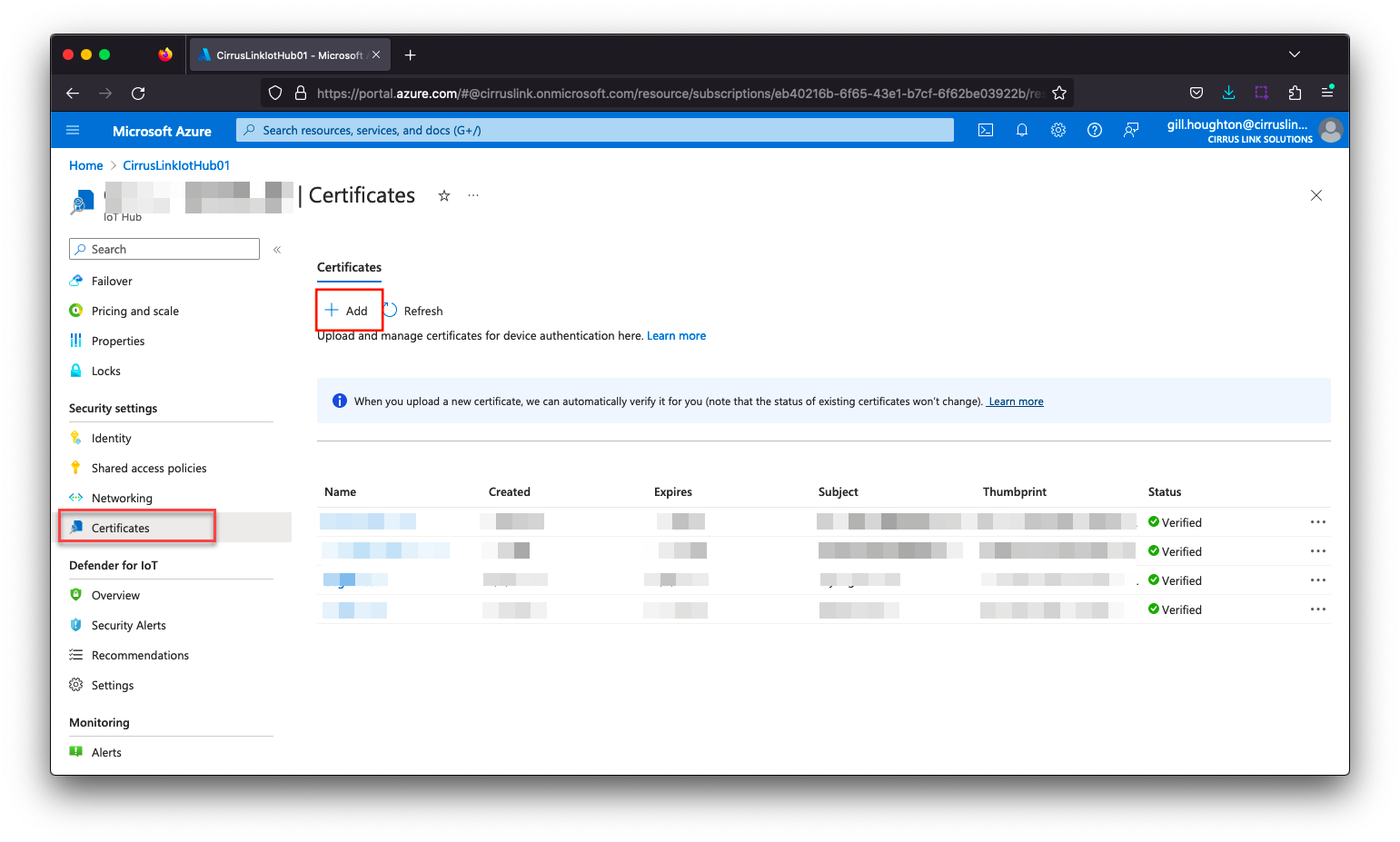
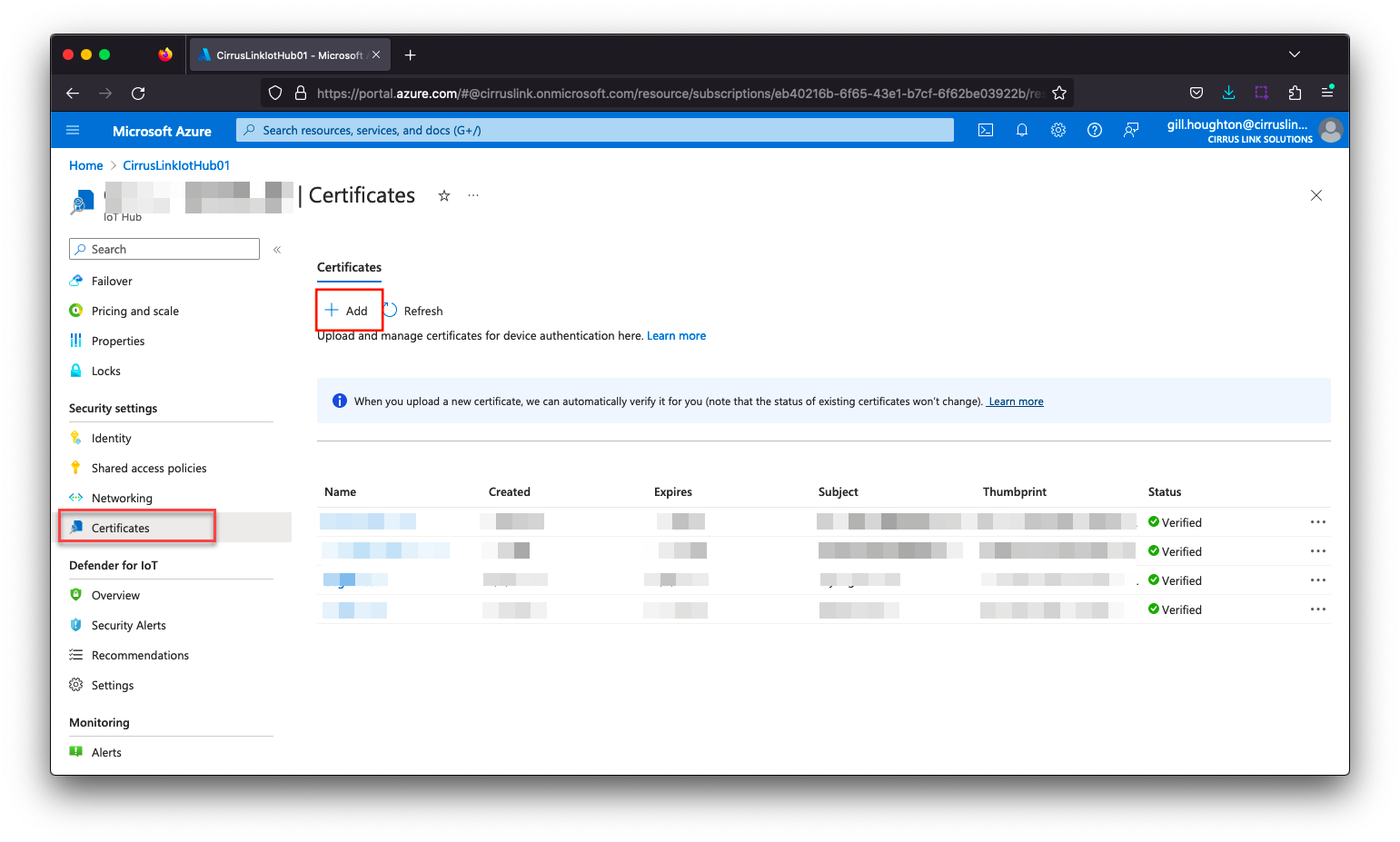
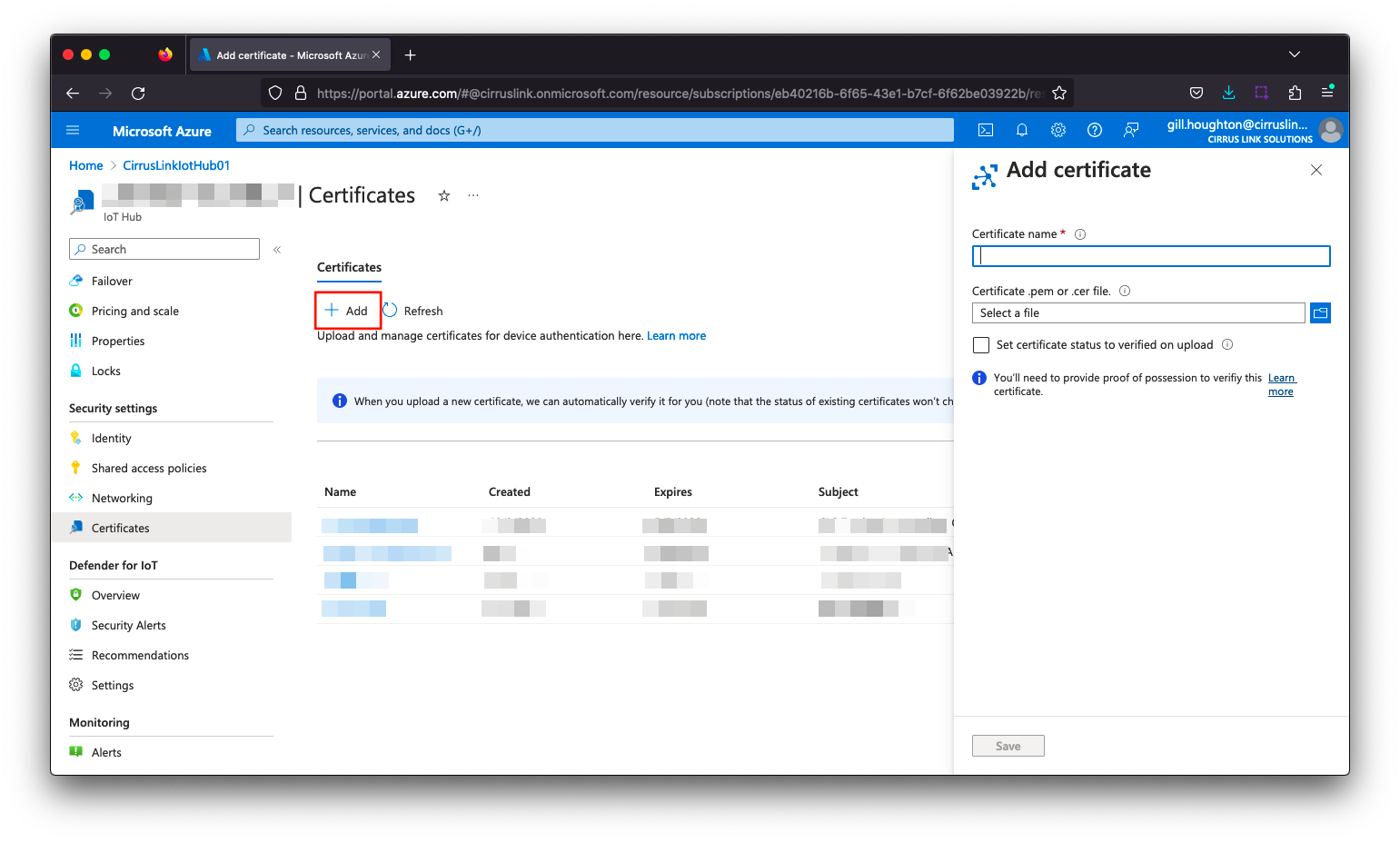
Add Root Certificate to IoT Hub
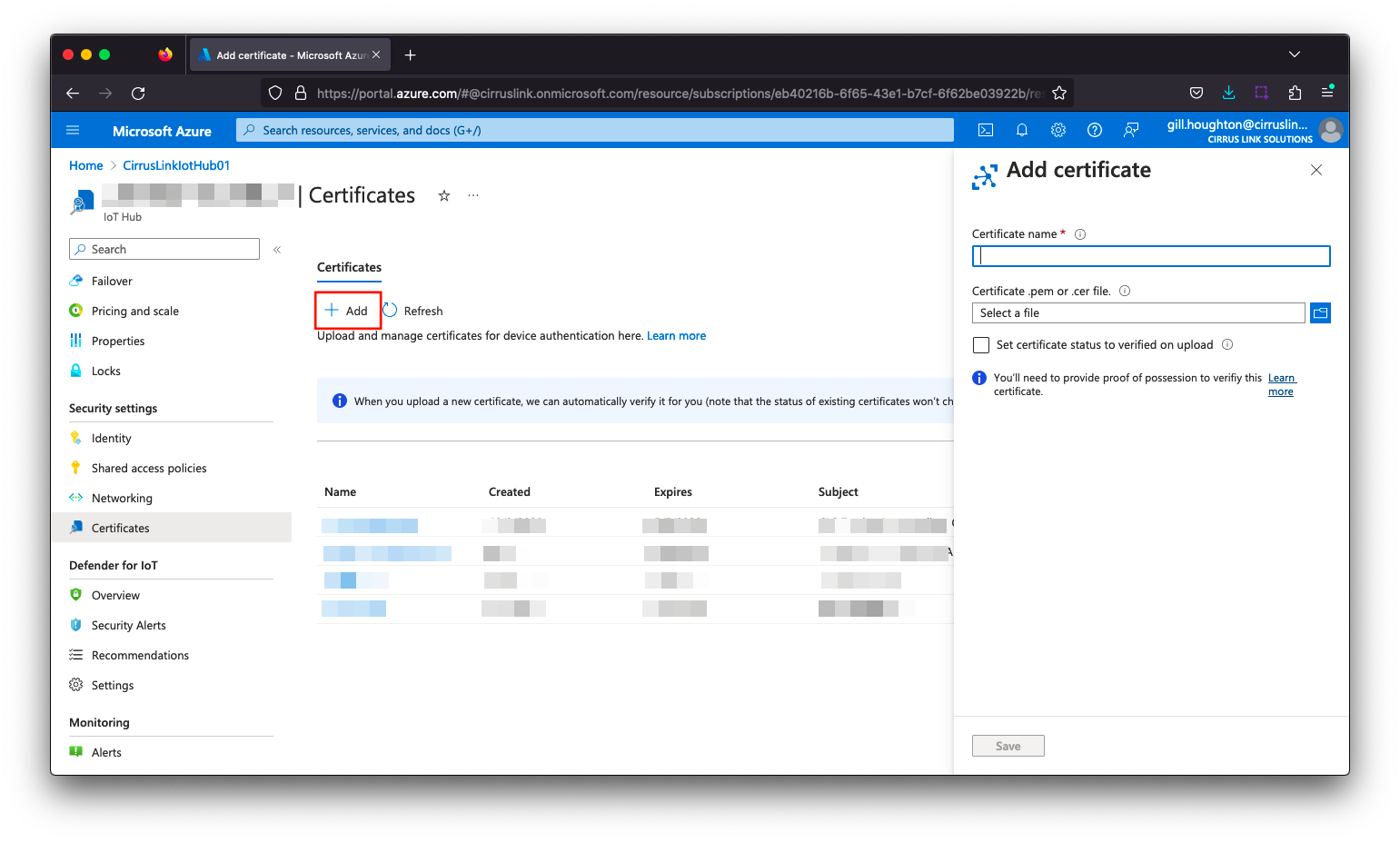
- On the IoT Hub resource Overview page, click “Certificates” menu on the left blade, and click the “Add” button.
- Give a certificate name (eg. MyOrg RootCertificate) and import the ca.pem file from your iotcerts/ca folder. Check the “Set certificate status to verified on upload” checkbox and click Save.
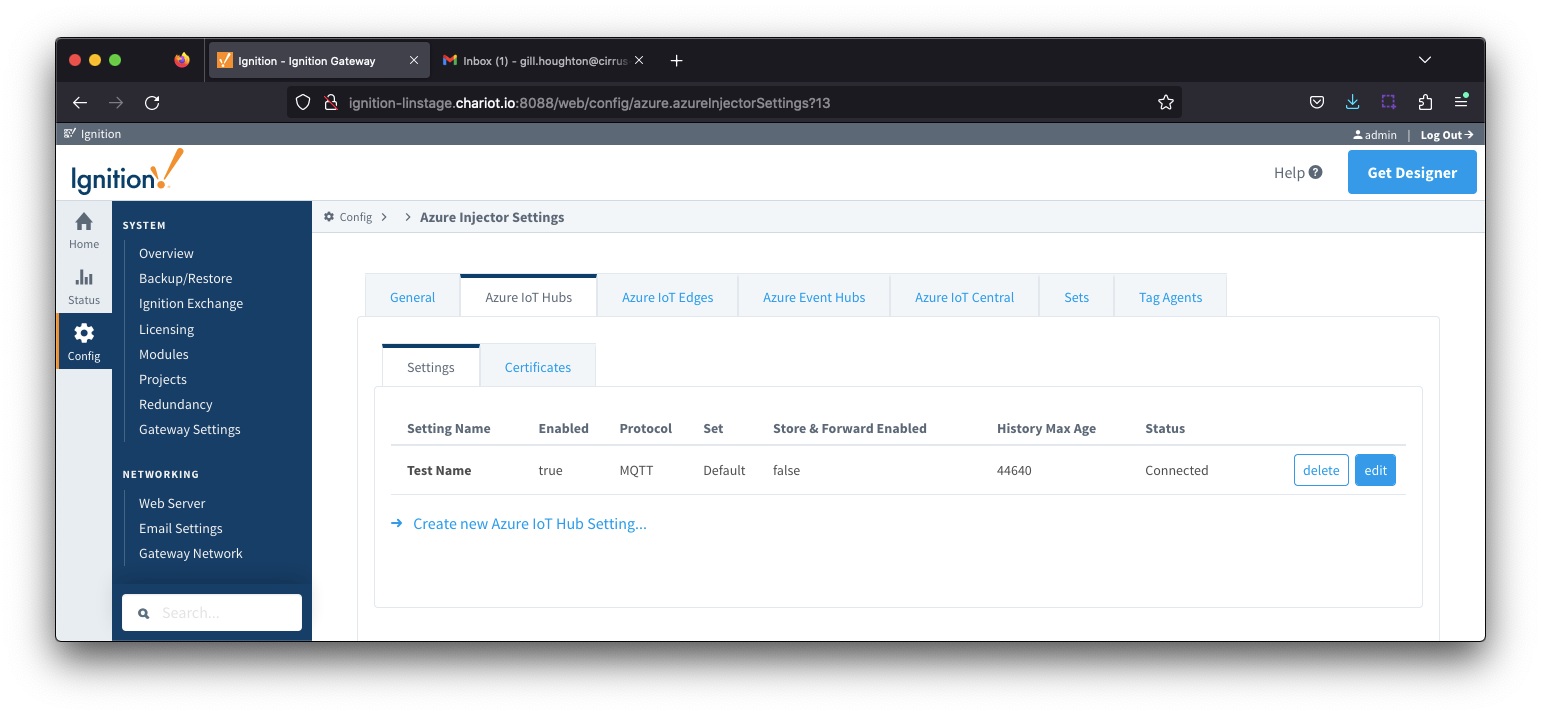
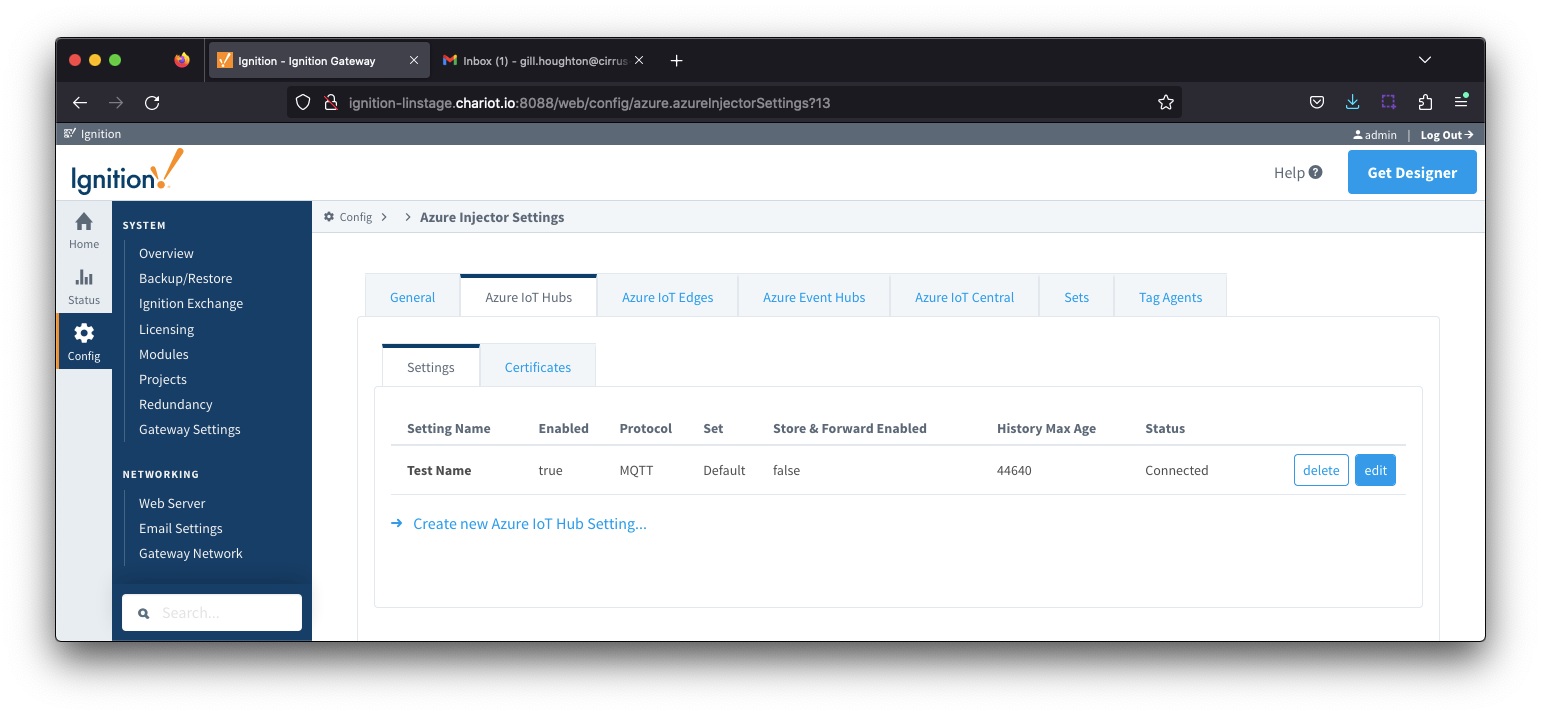
Add device certificates to Azure Injector IoT Hub configuration
Navigate to the Azure Injector > Settings > Azure IoT Hubs > Certificates and add the certificates as shown below:
| Friendly Name | Certificate Filename | File Description | File Location |
|---|
| CACertificate | |
|
|
| DeviceCertificate | CertDevice.pem | Device Certificate | iotcerts/certs/device/CertDevice.pem |
| DeviceKey | CertDevice.key | Device Private Key | iotcerts/certs/device/CertDevice.key |

Update the Azure Injector > Settings > Azure IoT Hubs > Settings configuration to use the certificates as shown below. Note : the certificates created do not use a Password

Verify the connection is established as shown by the Status on the Azure Injector > Settings > Azure IoT Hubs view
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()