| Anchor |
|---|
| create-keystore |
|---|
| create-keystore |
|---|
|
NOTE: The procedure below is only applicable when running pre-4.0.4 modules. Manually configuring MQTT Distributor to consume a Java Keystore is supported and will work properly when running pre-4.0.4 modules, but it is no longer the recommended process for encrypting MQTT communication. If possible, please upgrade to modules version 4.0.4 or higher and follow the default workflow to secure MQTT communication.
Whether you are using a certificate issued by a trusted CA (Certificate Authority) or a self-signed certificate, internally MQTT Distributor accesses these certificate(s) via the Java KeyStore file that it is configured to use. This KeyStore must contain the public certificate, the private key, and possibly an intermediate certificate if applicable.
...
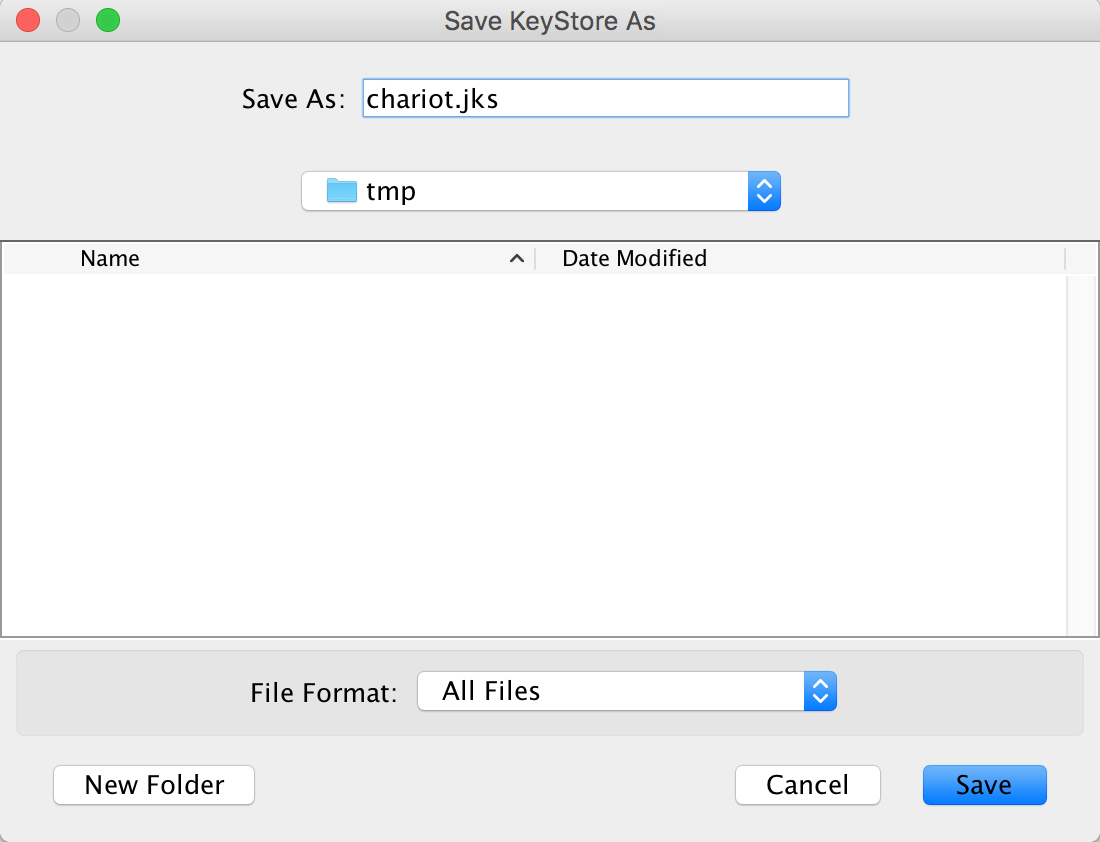
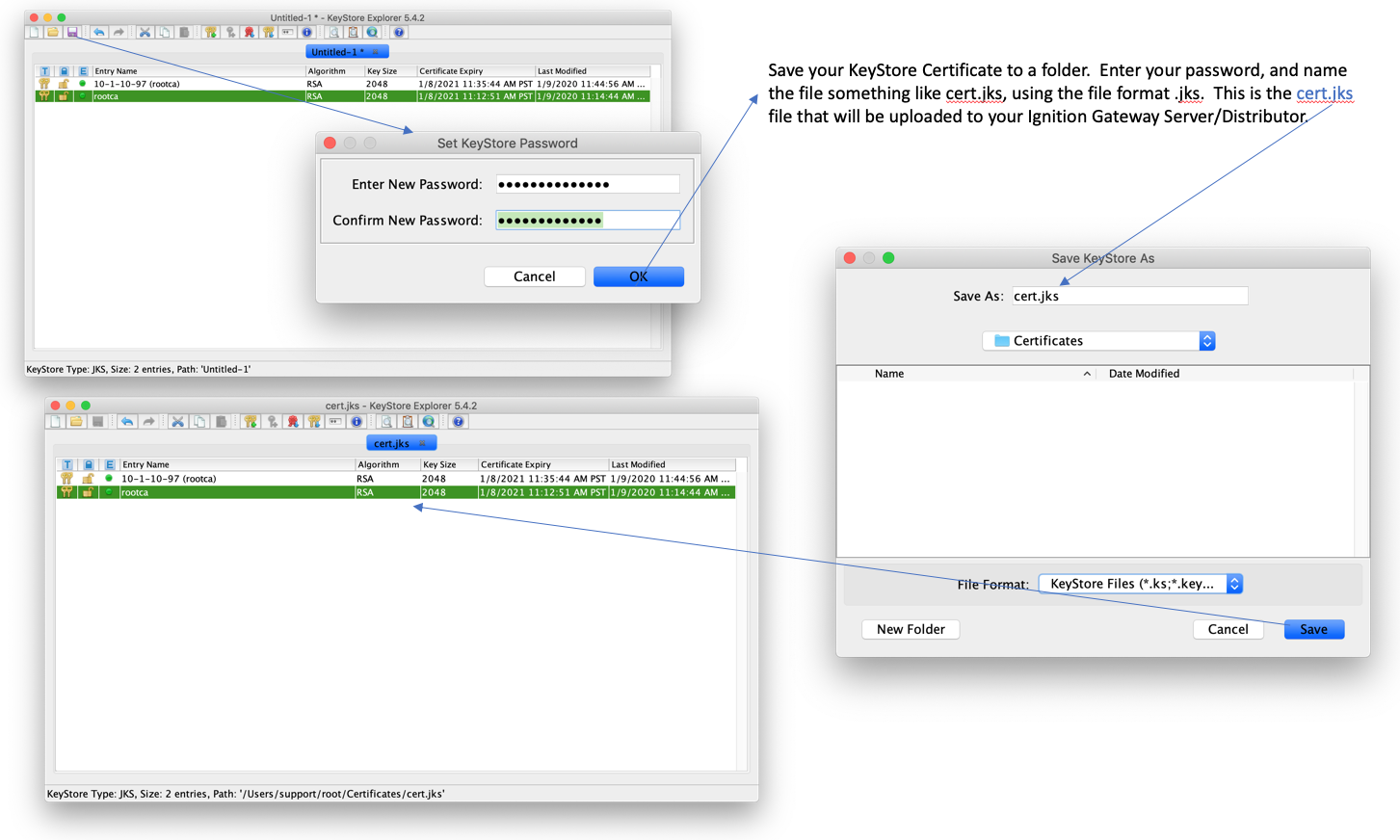
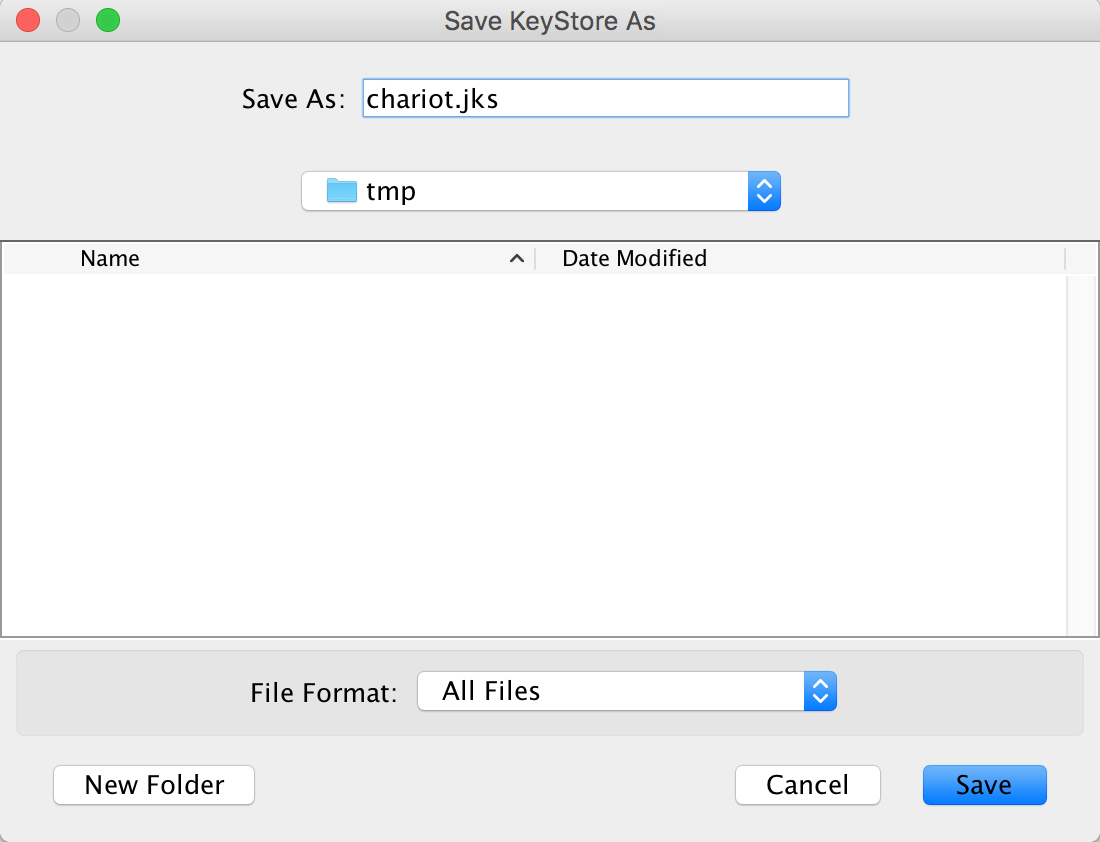
Finally, give it a name and location on the filesystem and click Save:
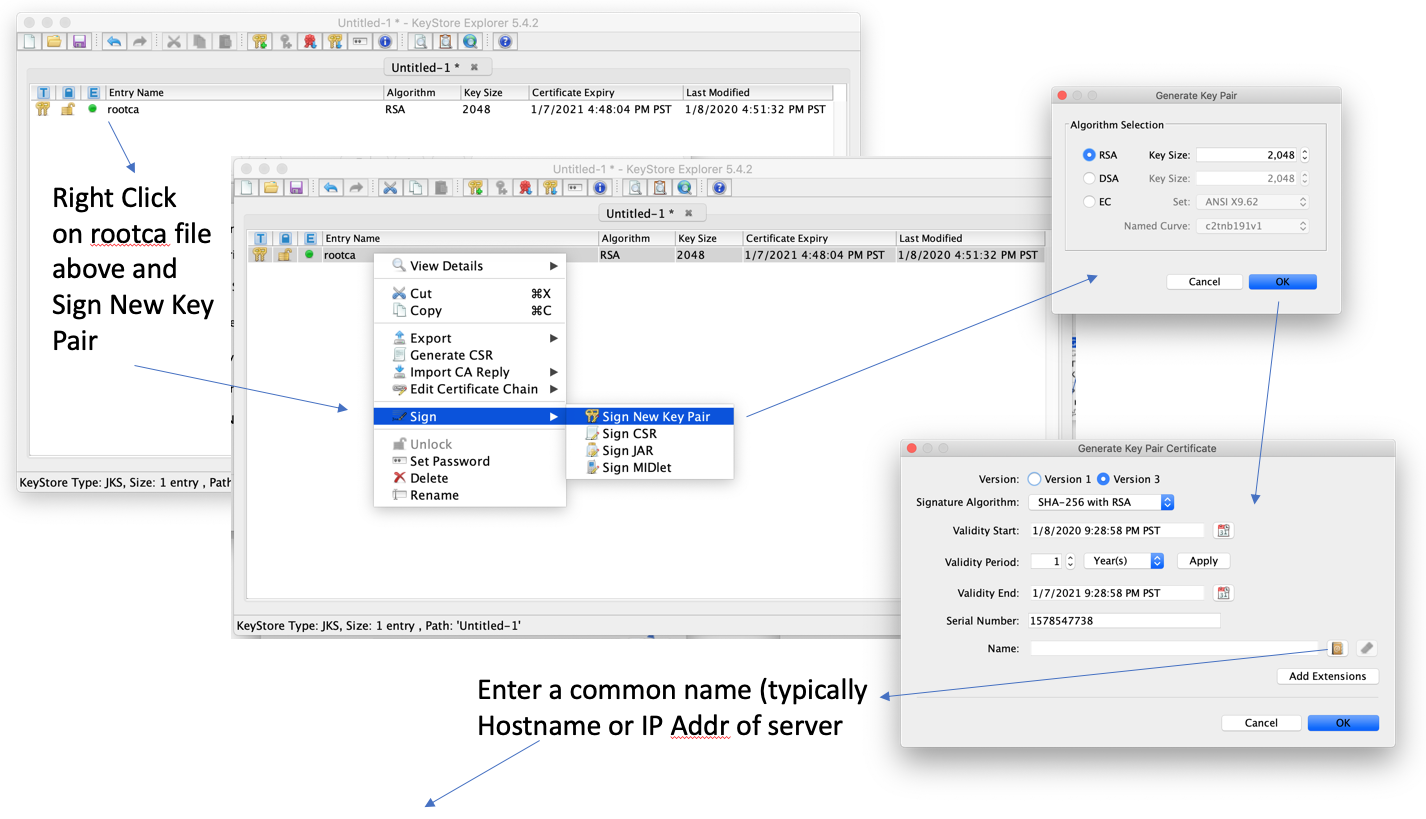
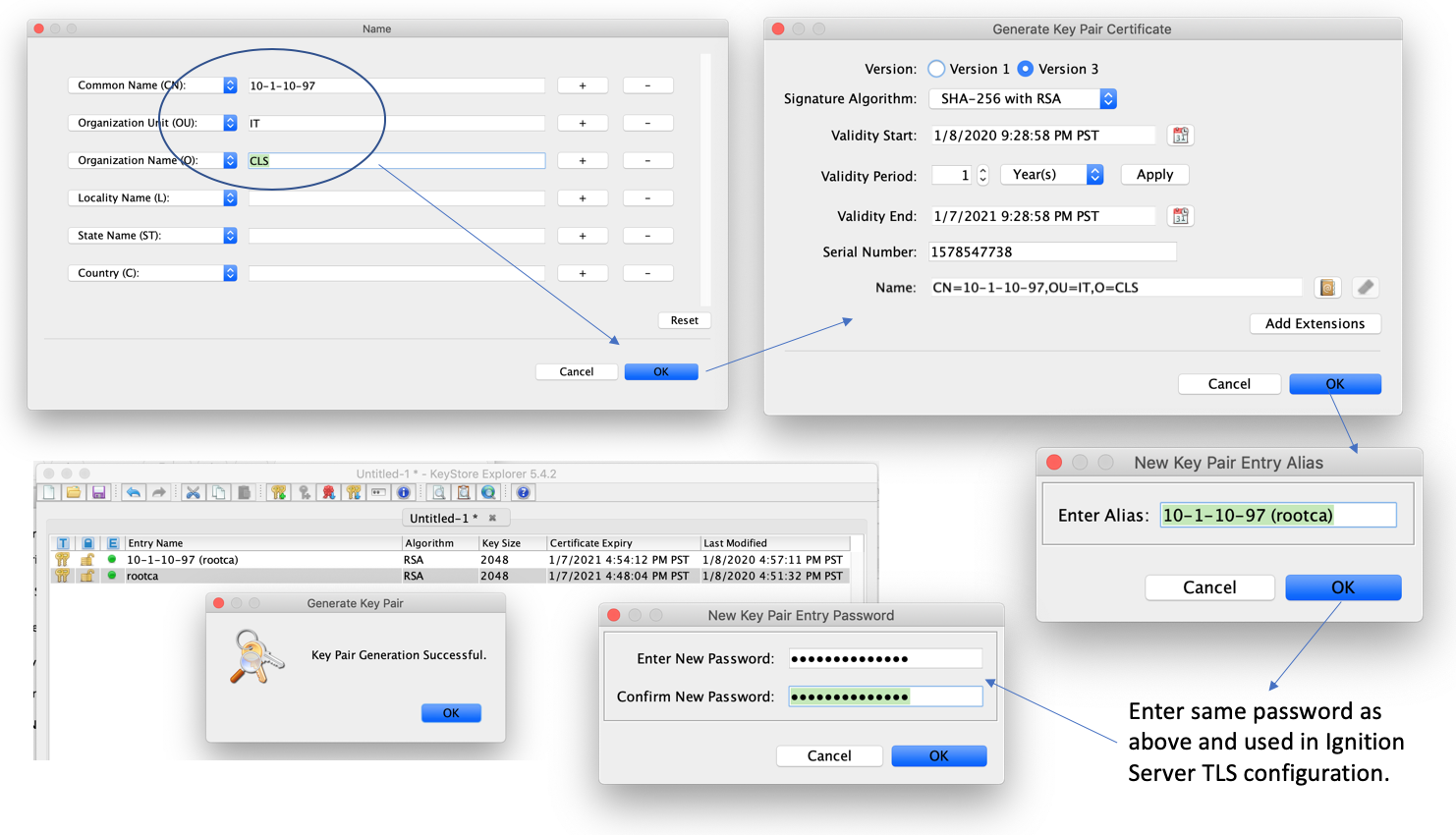
Generate a Private Key Pair
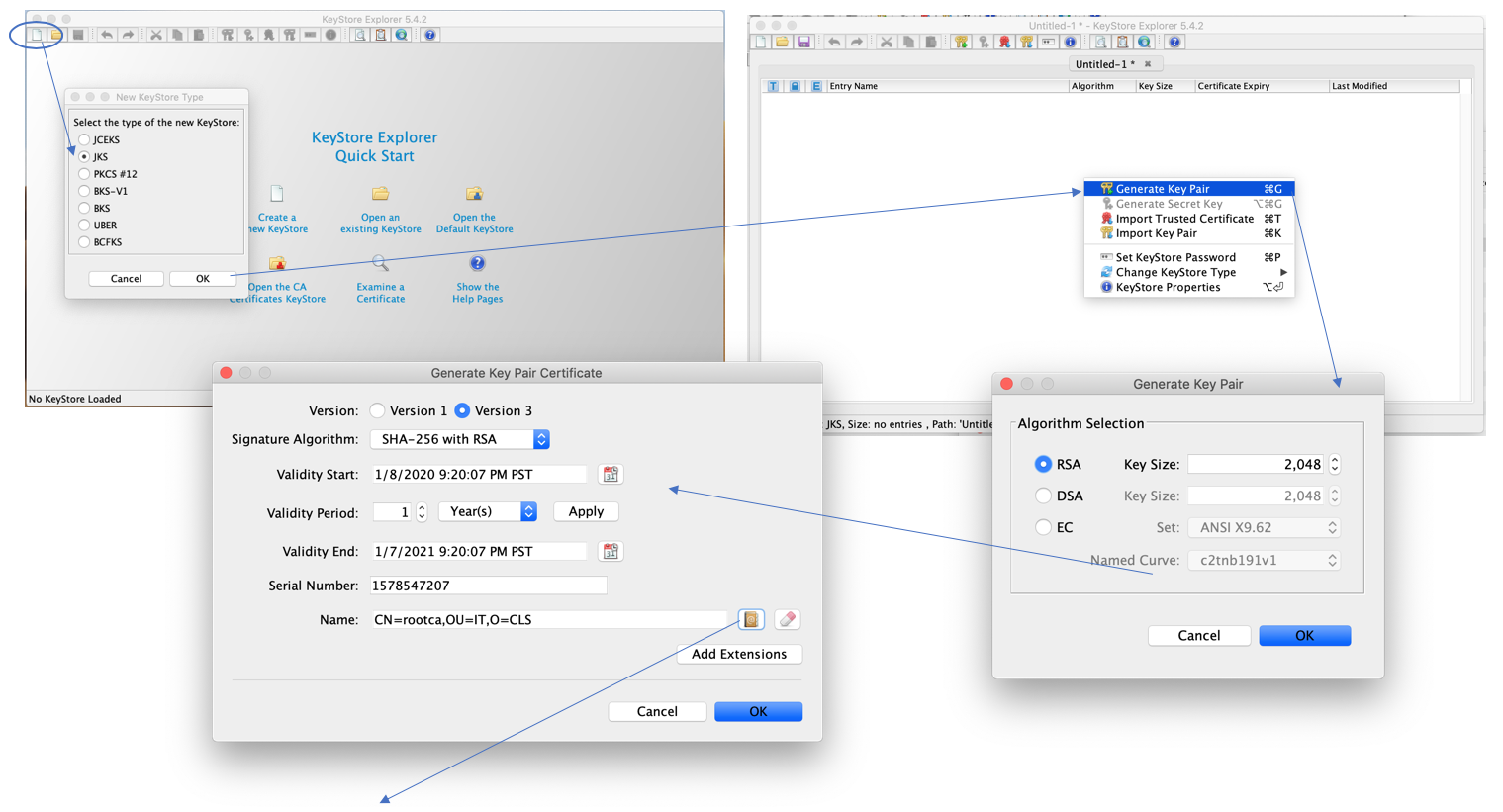
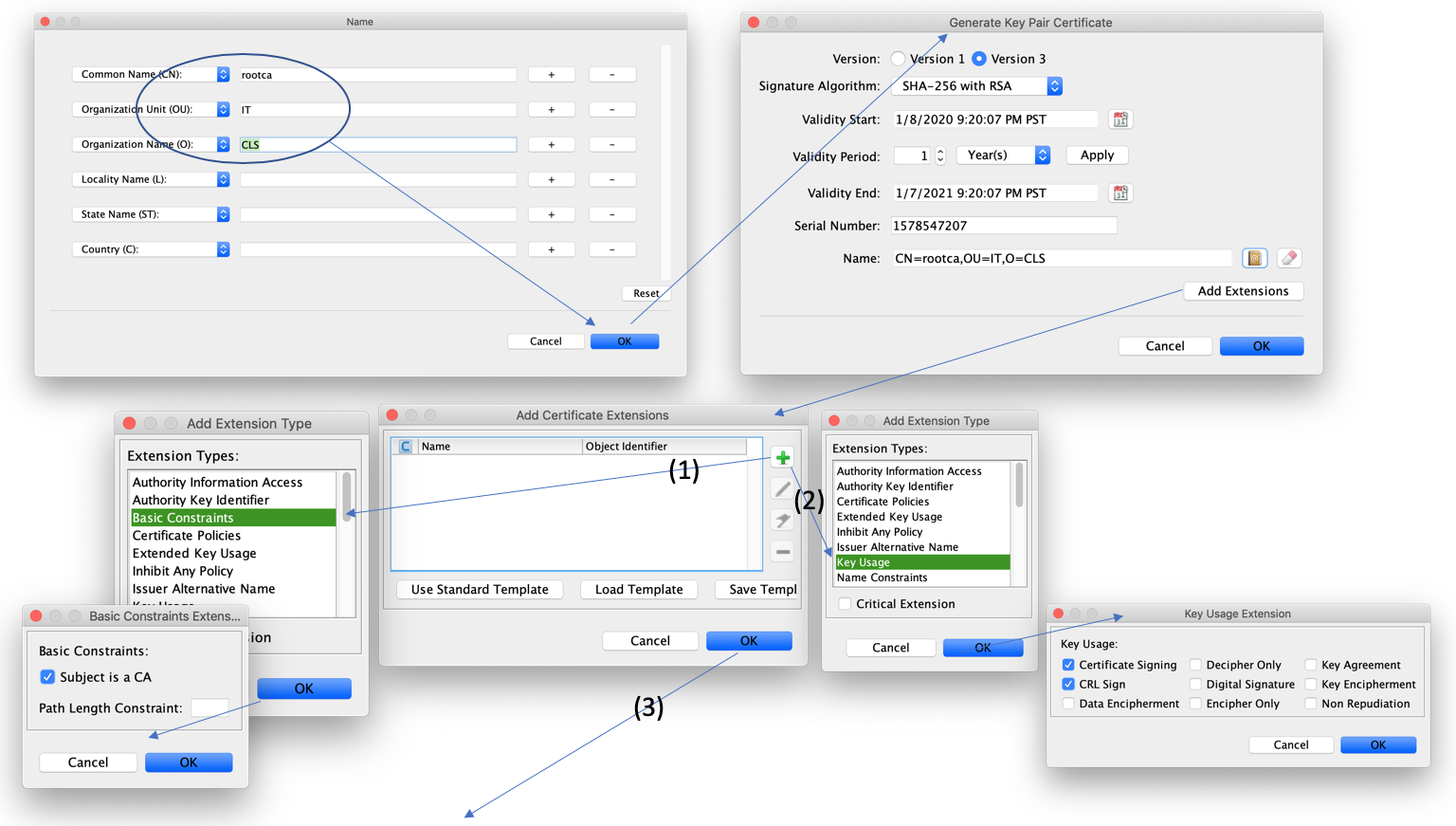
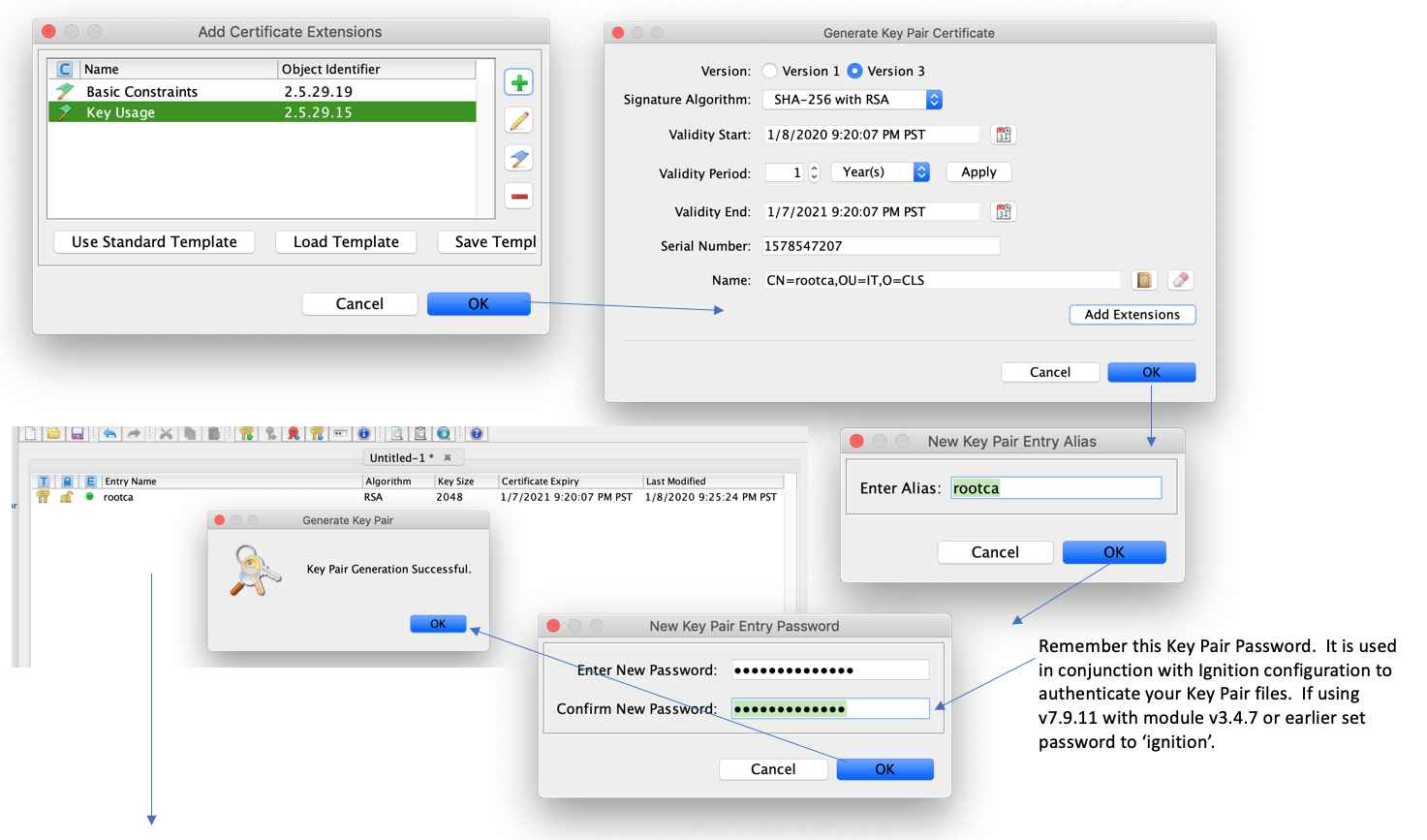
If you prefer TLS connection over private networks you may instead generate your own Private Key Pair. Launch KeyStore Explorer and select 'Create a new KeyStore' of the type 'JKS', then [ OK]. In the background of the Untitled-1 page right click and select 'Generate Key Pair' as below:
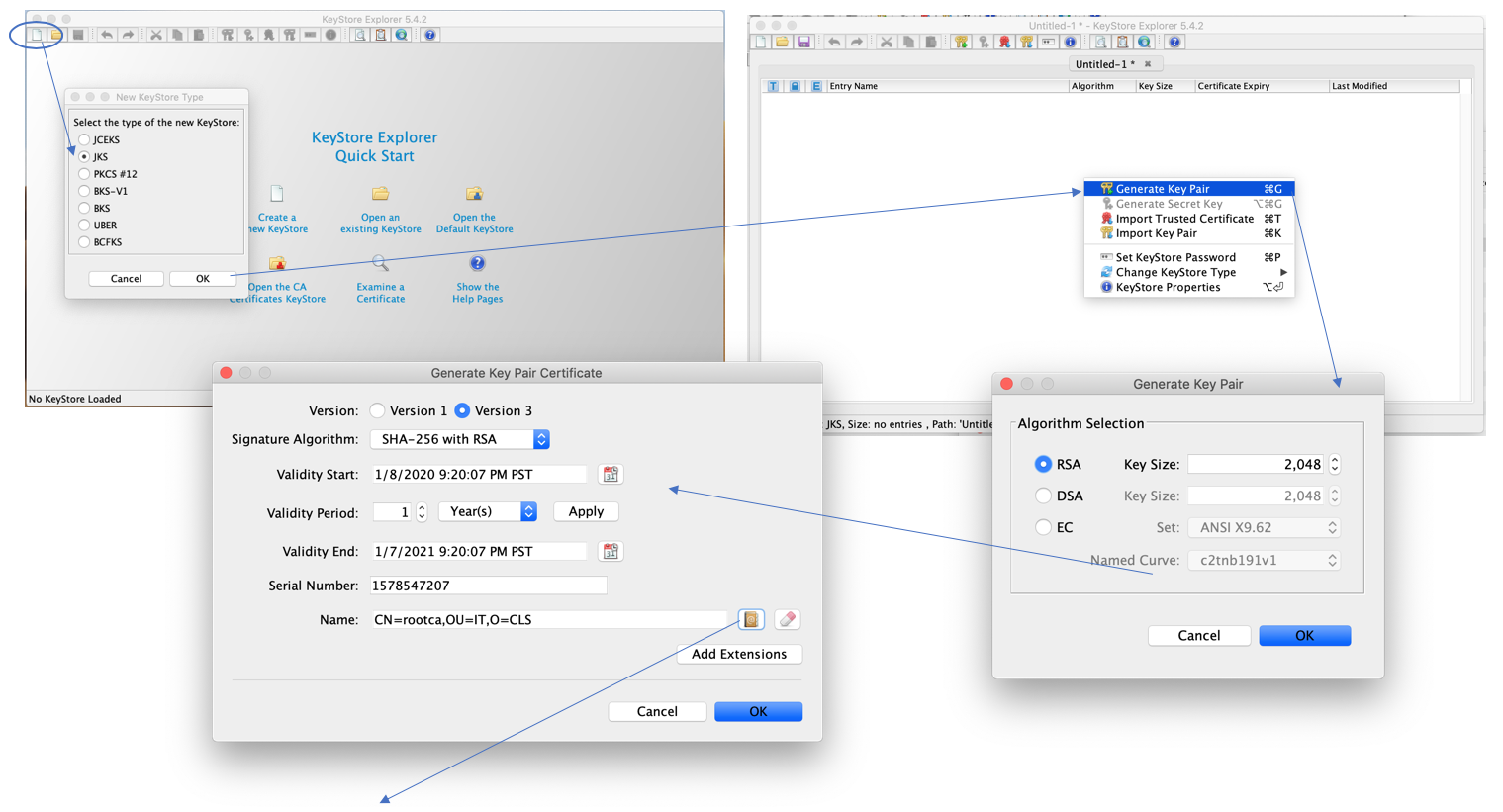 Image Removed
Image Removed
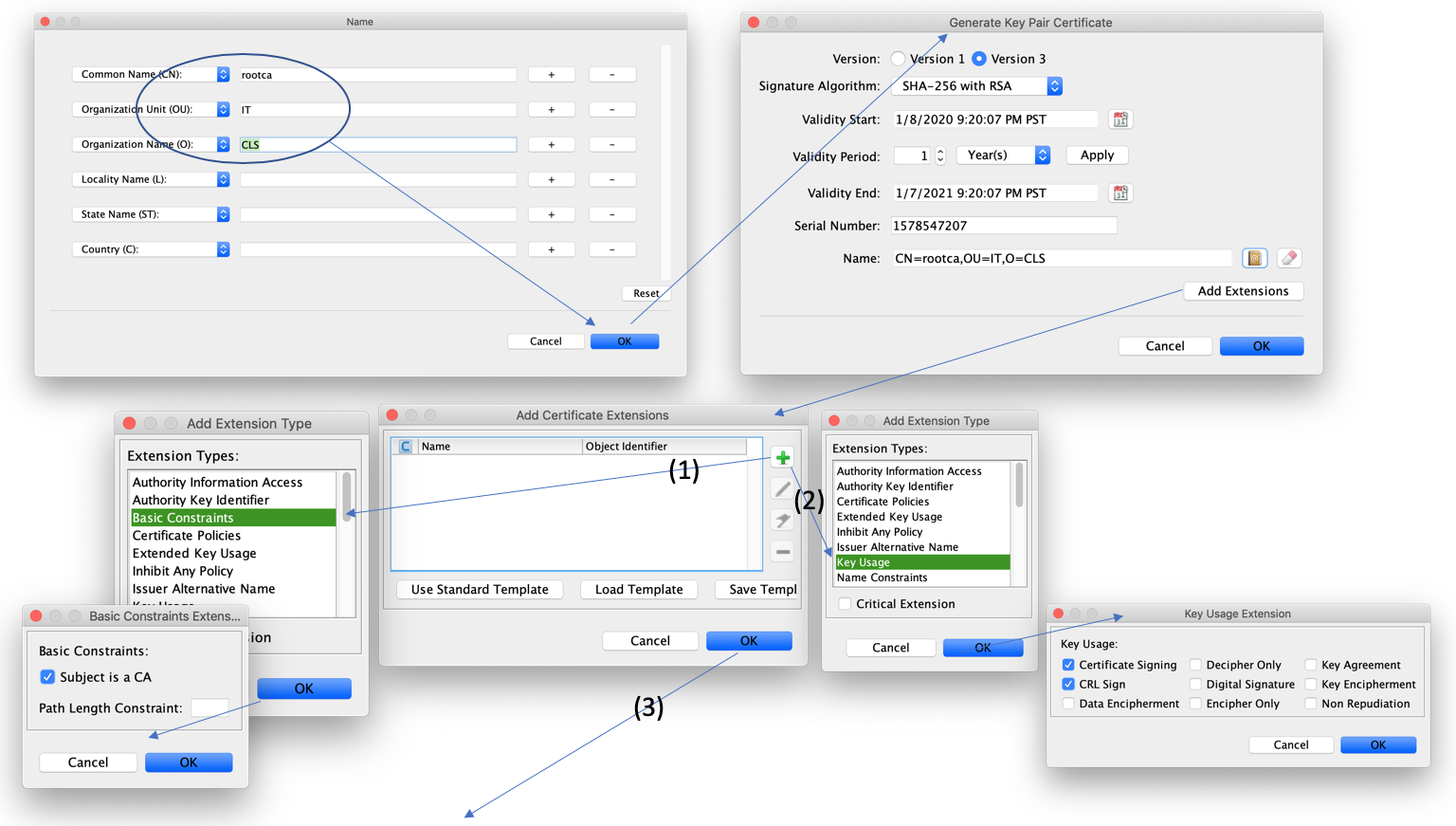 Image Removed
Image Removed
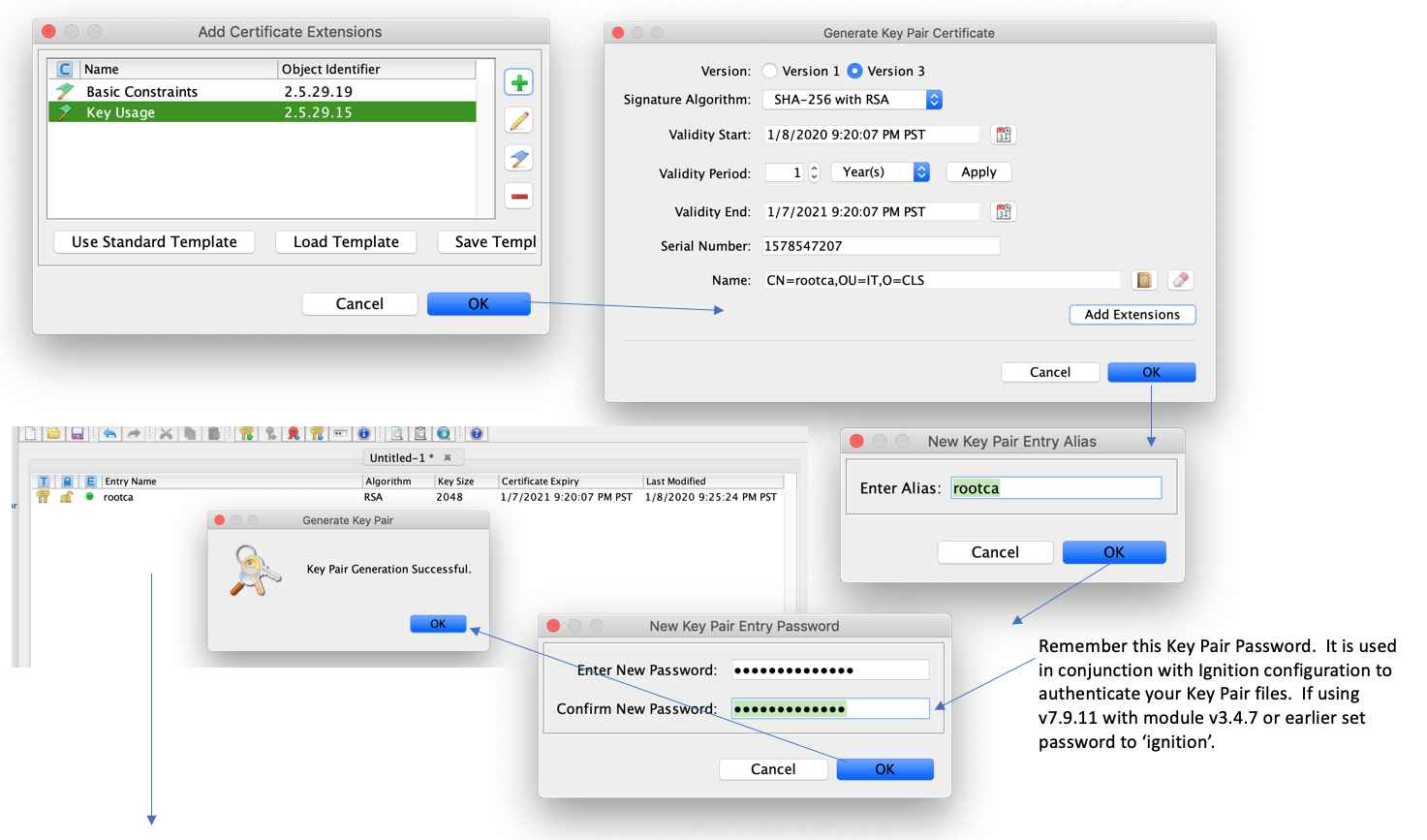 Image Removed
Image Removed
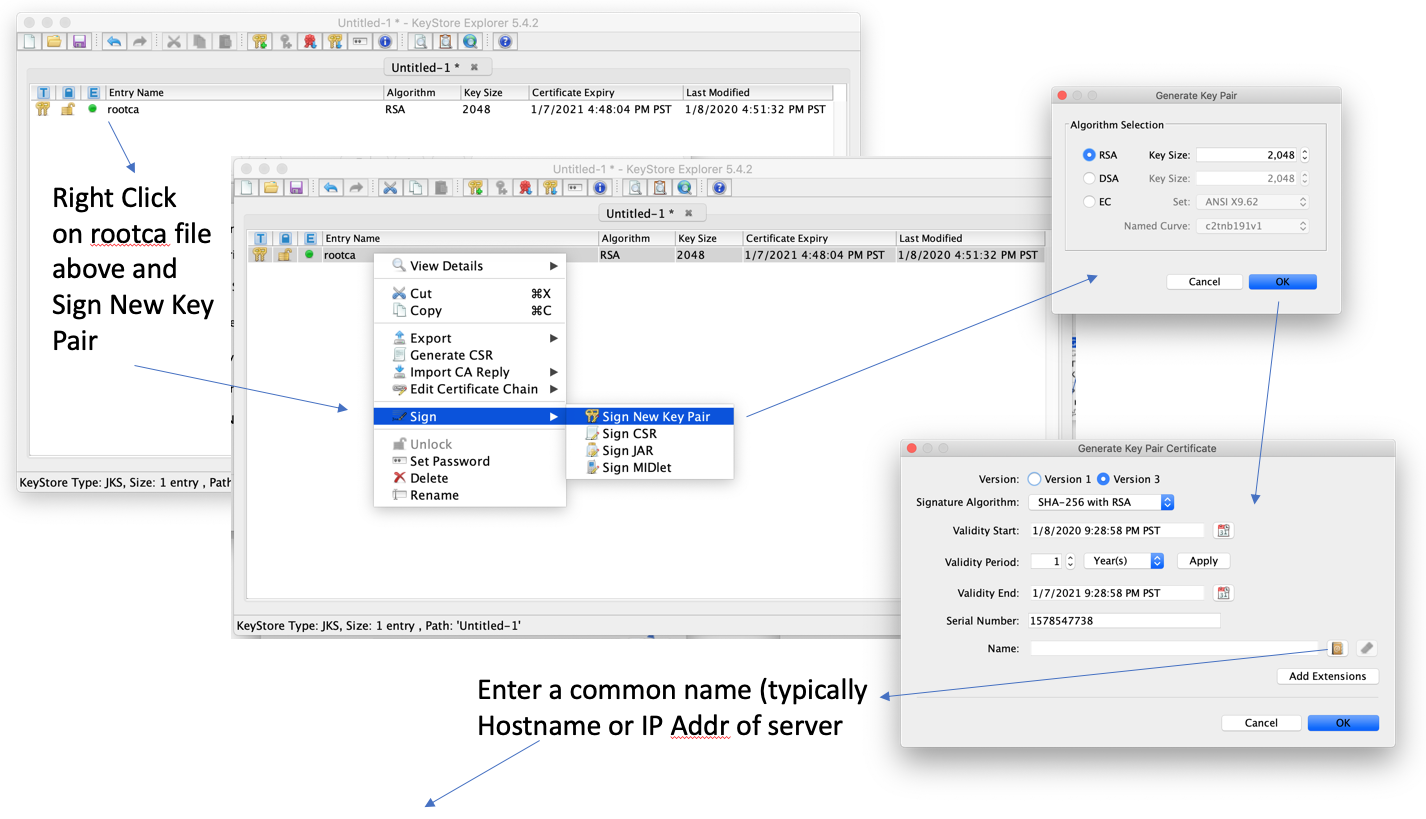 Image Removed
Image Removed
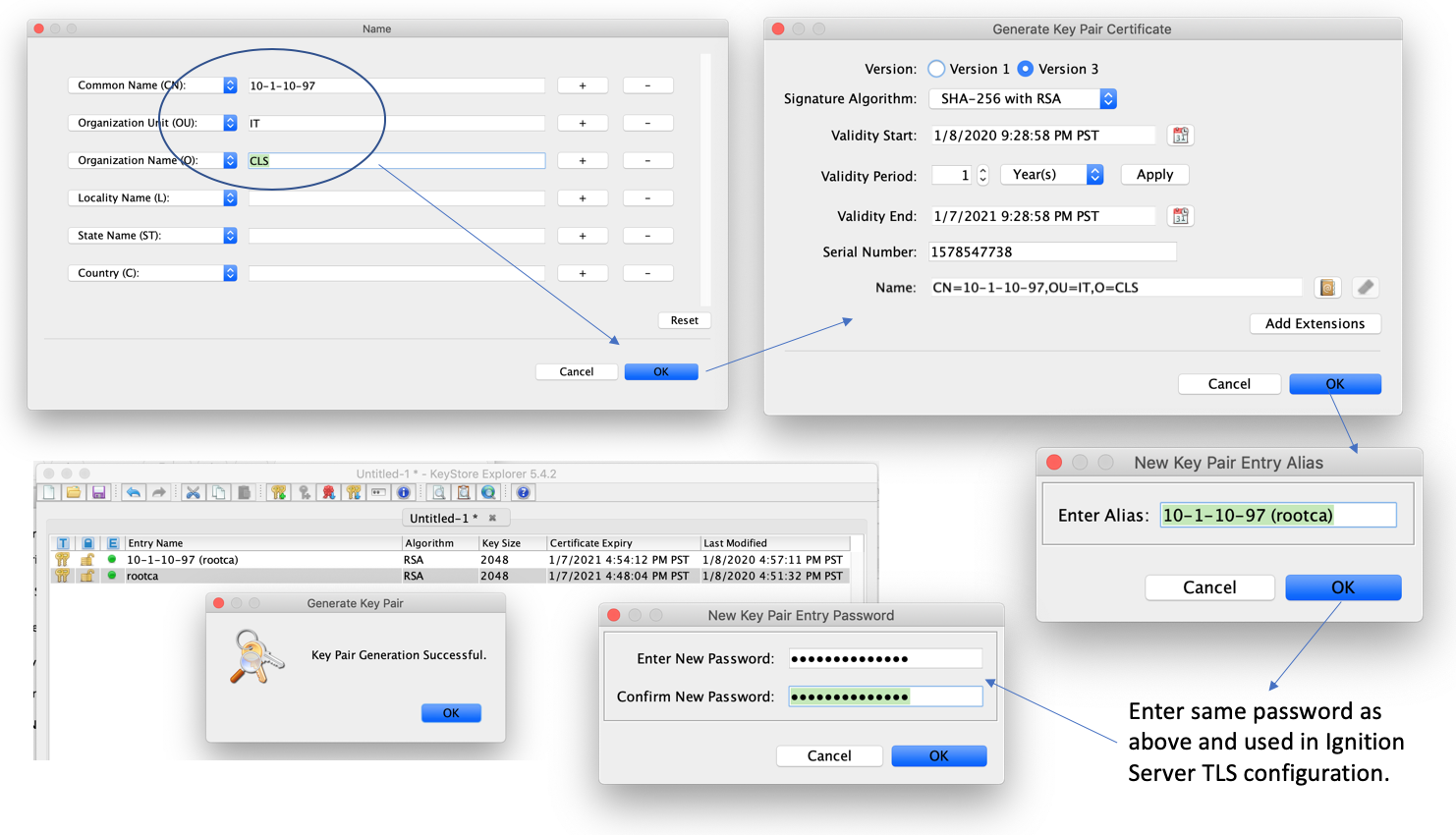 Image Removed
Image Removed
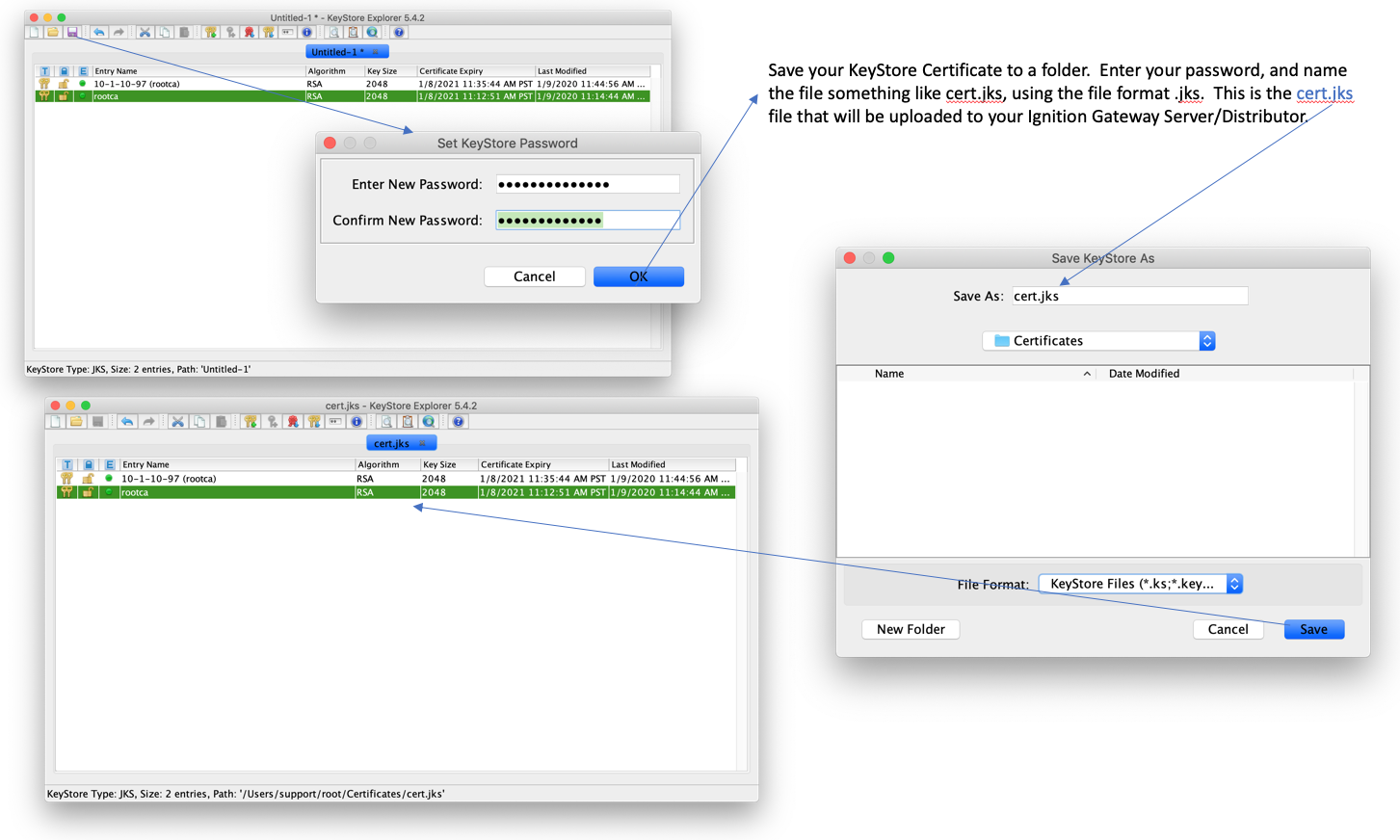 Image Removed
Image Removed
Configuring MQTT Distributor to use a Keystore
...
Export the Certificate Chain for Client-side Use (self-signed certs only)
| Anchor |
|---|
| export-cert-chain |
|---|
| export-cert-chain |
|---|
|
If using self-signed certificates, the required CA certificates are not known to MQTT clients by default as they would be if the certificate was generated by a real CA. This requires one to acquire and upload the CA certificates that make up the certificate chain (aka. "chain-of-trust"). The certificate chain can be exported from an existing keystore (like the one created here) using the steps below. Return to the KeyStore Explorer application and generate the necessary root.ca.pem file. Save this file in same location (by default) as your cert.jks file. Use this template below to upload this root.ca.pem file to Transmission and Engine. (Password not required on these pages.)
...
Once the settings are saved, the MQTT client associated with MQTT Engine or MQTT Transmission will connect using TLS.
Additional Resources
- Inductive Automation's Ignition download with free trial
- Azure Injector download with free trial
- Questions about this tutorial?
- Sales questions
- About Cirrus Link
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()