...
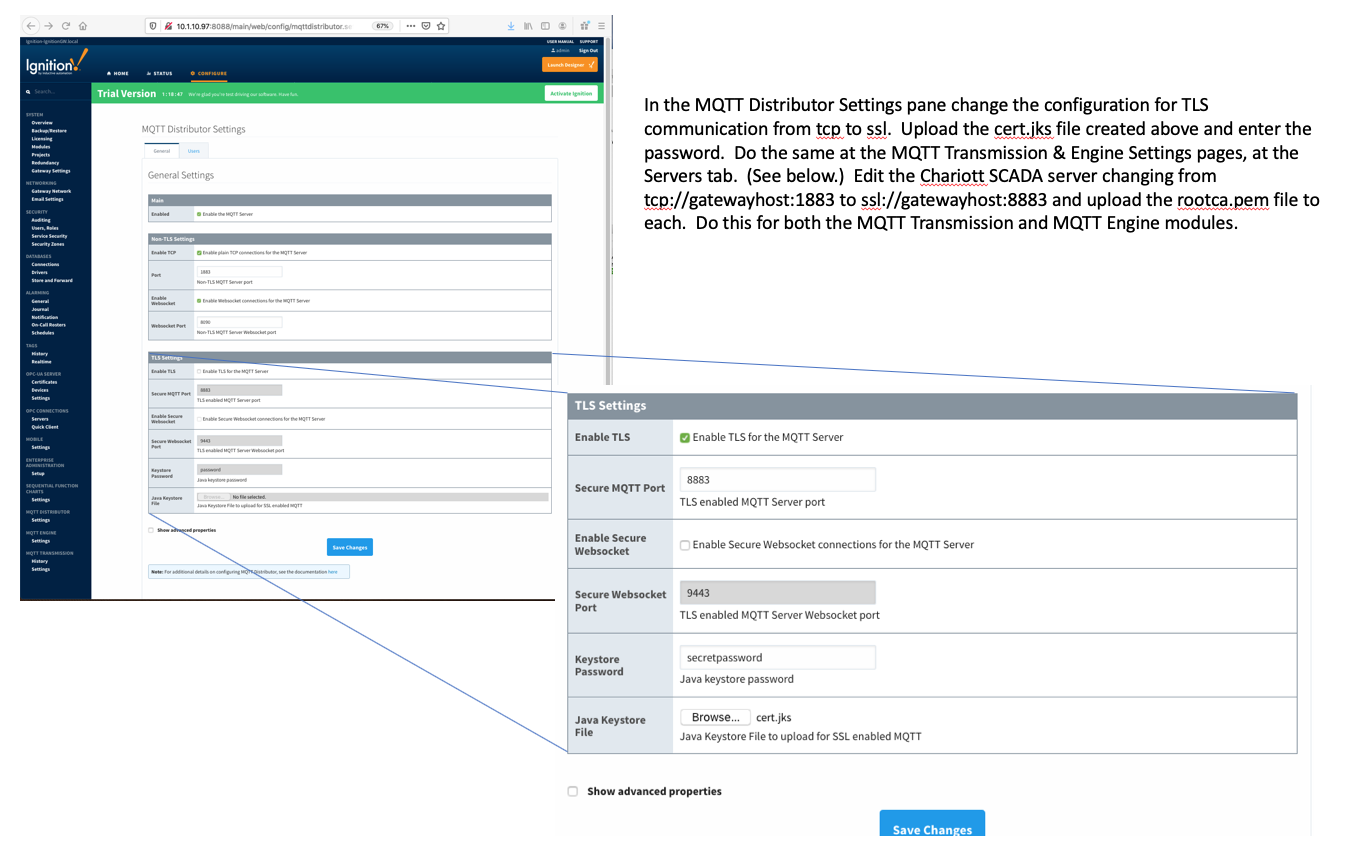
In the MQTT Distributor Settings change the configuration for TLS communication from TCP to SSL. Upload the cert.jks file created above and enter the password. Image Removed
Image Removed
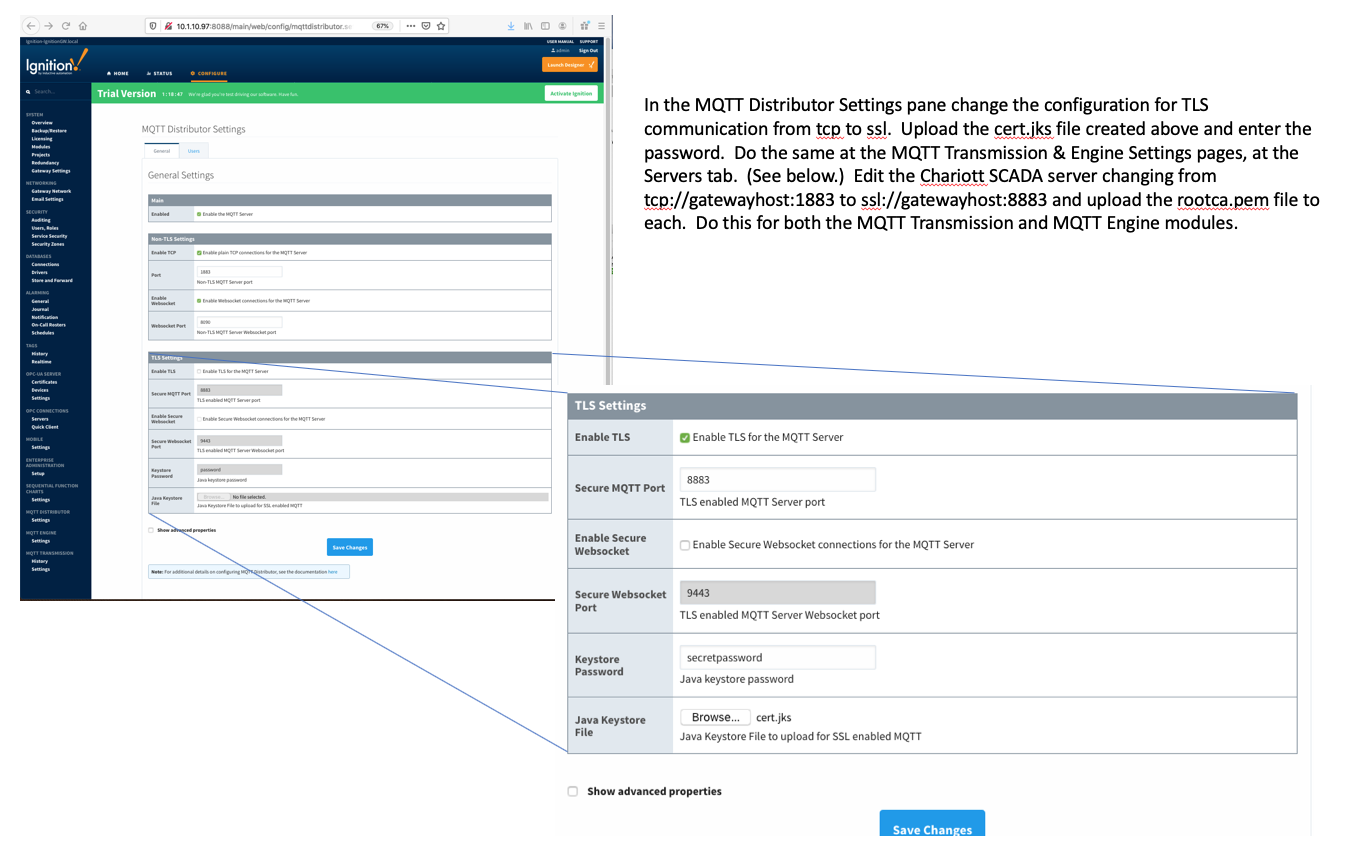 Image Added
Image Added
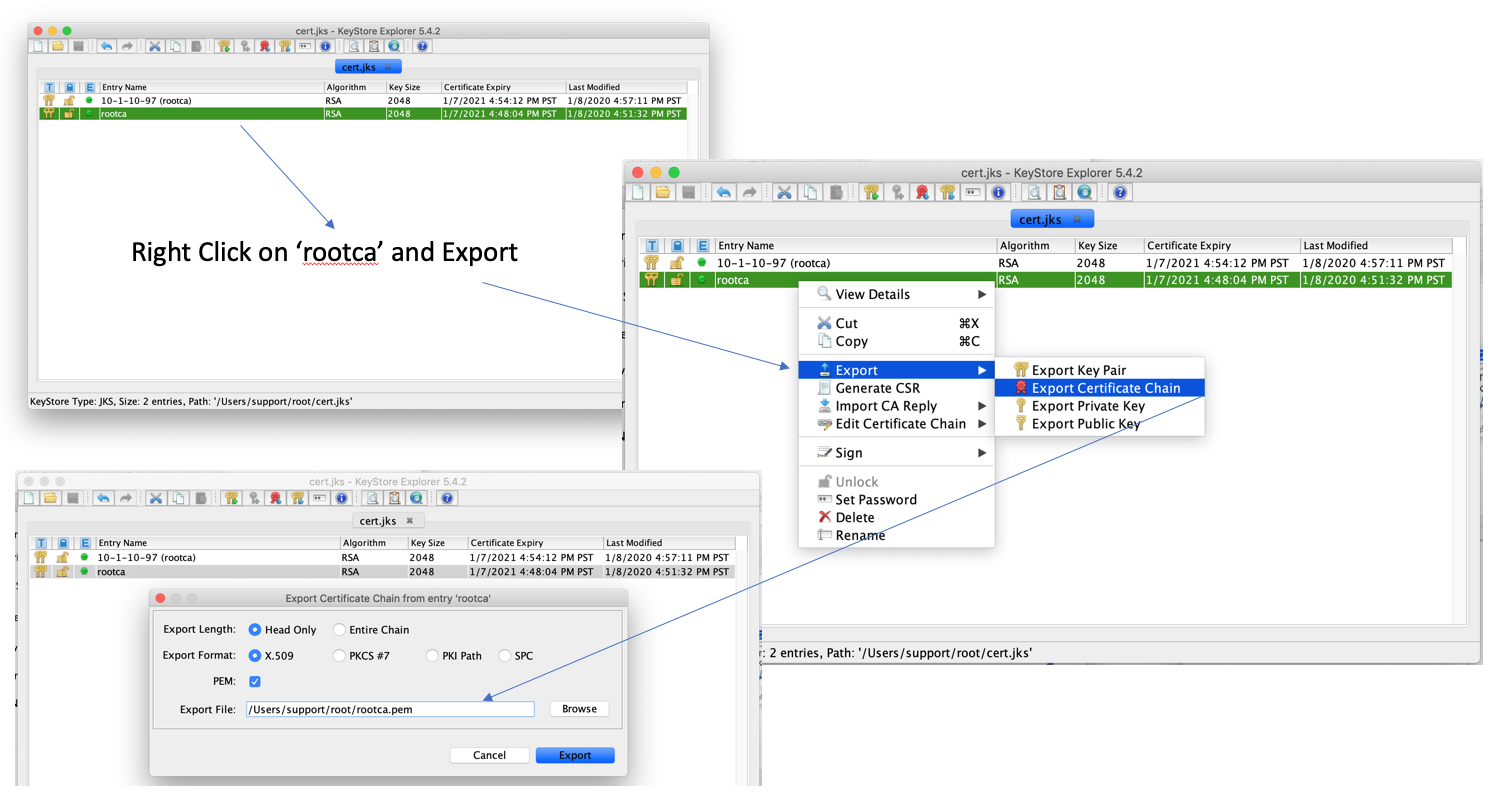
Generate rootca.pem file: Return to your KeyStore Explorer application and generate the necessary root.ca.pem file. Save this file in same location (by default) as your cert.jks file. Use this template below to upload this root.ca.pem file to Transmission and Engine. (Password not required on these pages.)
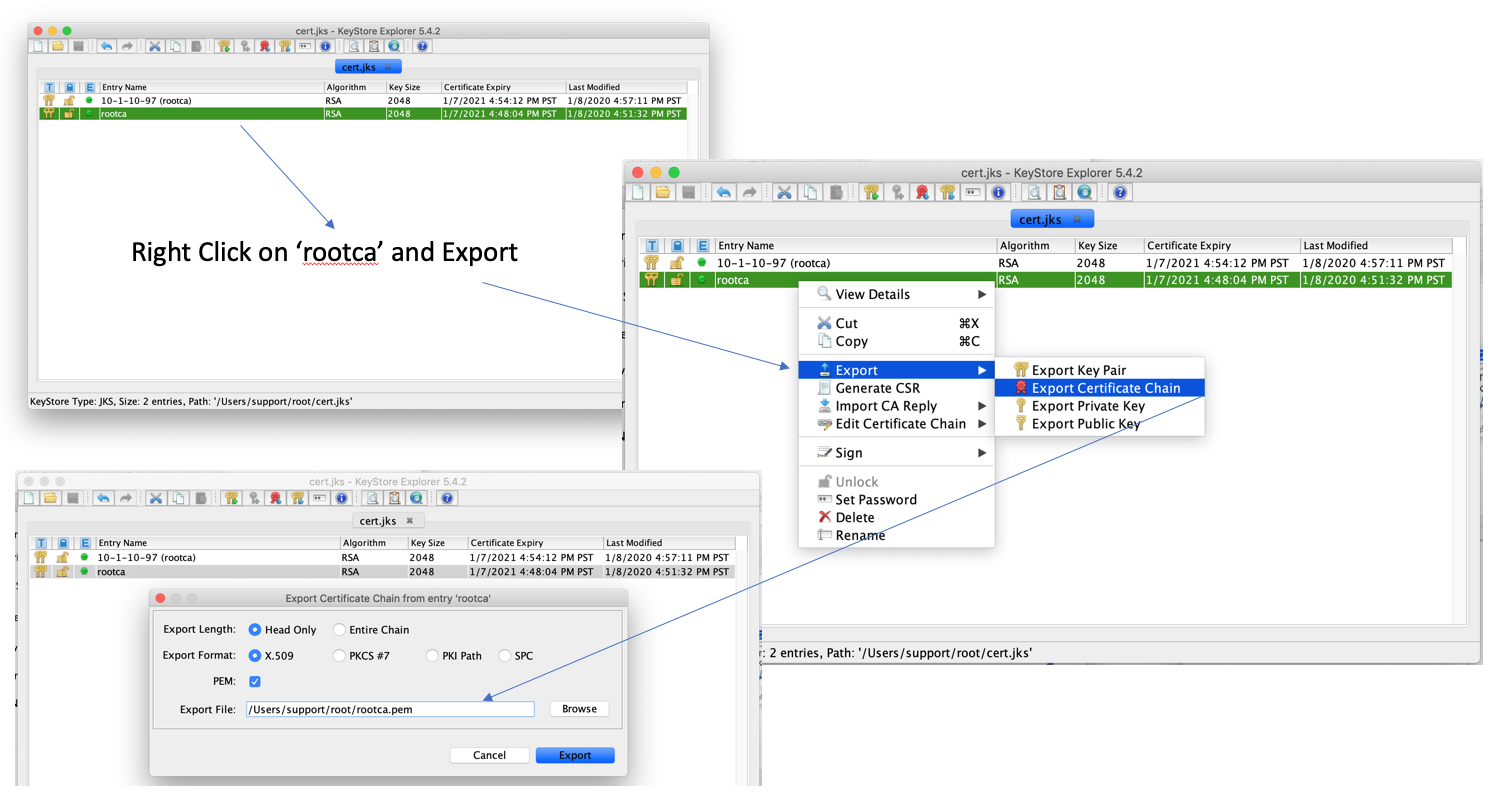 Image Added
Image Added
Save this rootca.pem key file. This will be installed on both Engine and Transmission Modules to allow and connect securely via SSL protocol to your Distributor (Ignition Server).
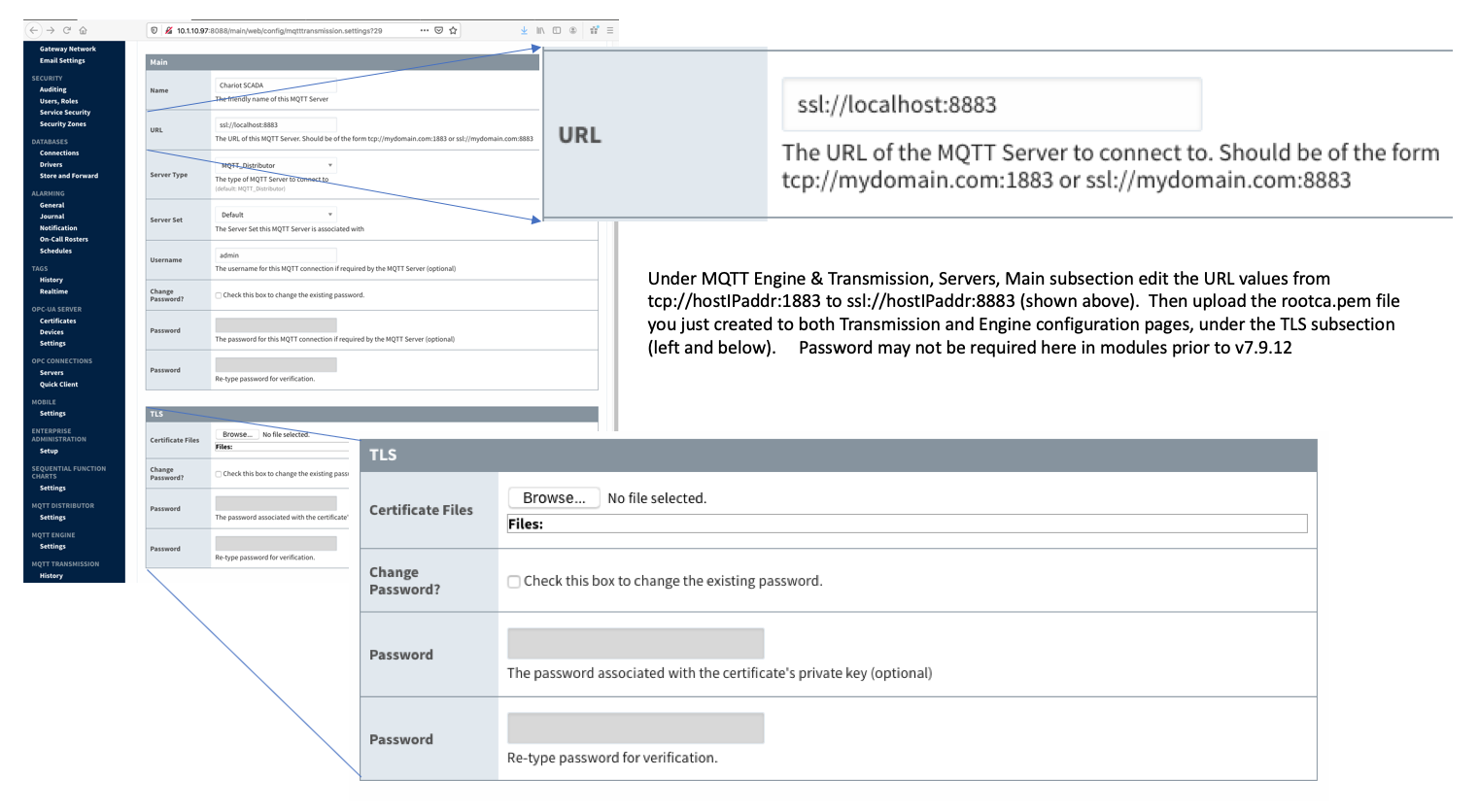 Image Added
Image Added
At this point, all MQTT clients can now connect over TLS enabled connections. Note the new port of 8883. If using a certificate signed by a publicly trusted CA and the OS with the MQTT client supports that specific CA, the clients don't have to make any modifications to their list of trusted root certificates. If using a self-signed certificate there are a couple options:
The root CA cert can be added to the Operation System's list of trusted root certificates
This means the application doesn't need to handle special cases (i.e. modifications to the Java Truststore)
The client side application can be modified to load the root CA certificate to validate the server certificate against
This doesn't require OS changes
Note if your certificate also requires an intermediate certificate, this must also be added to the MQTT client so the full chain of trust can be established.
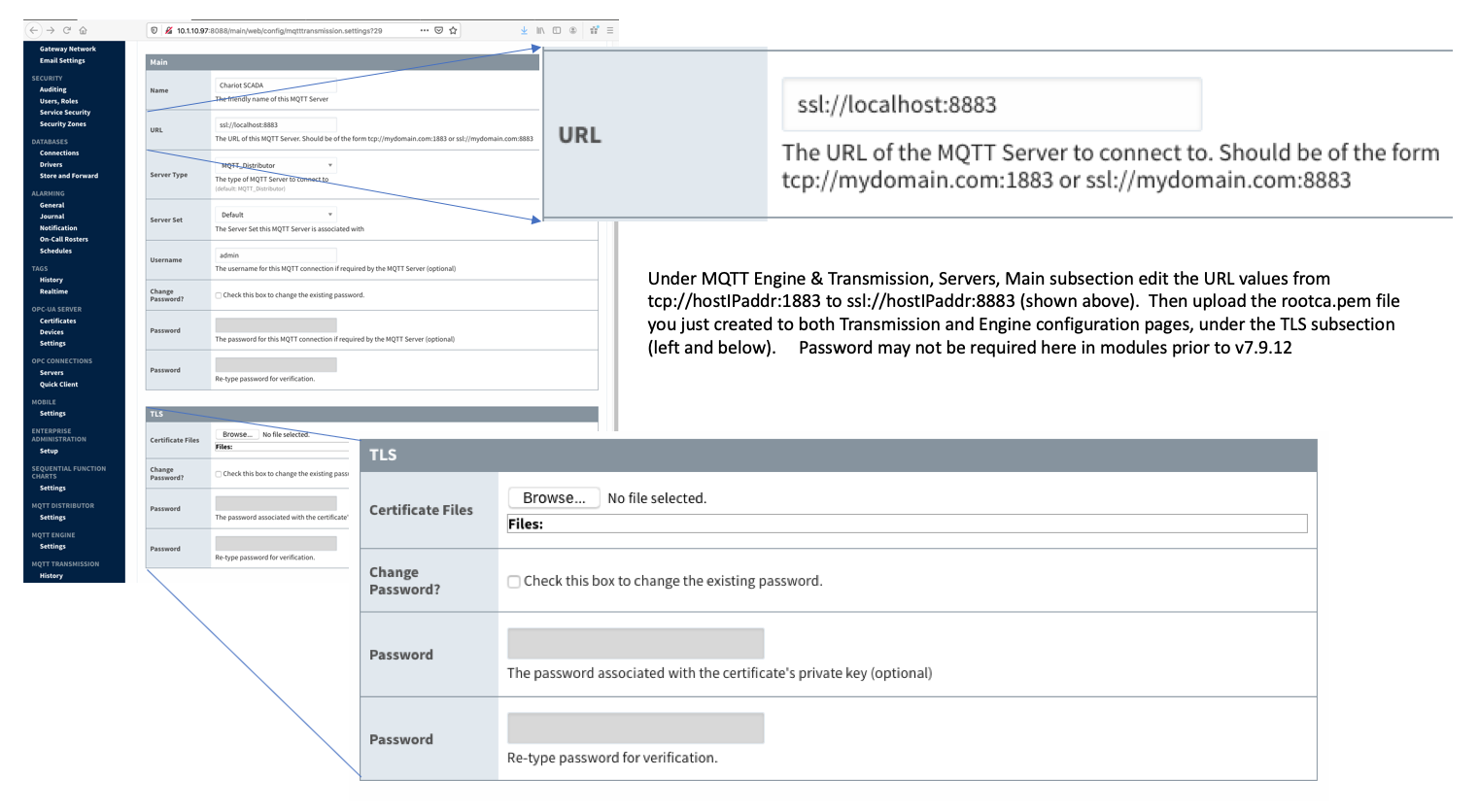
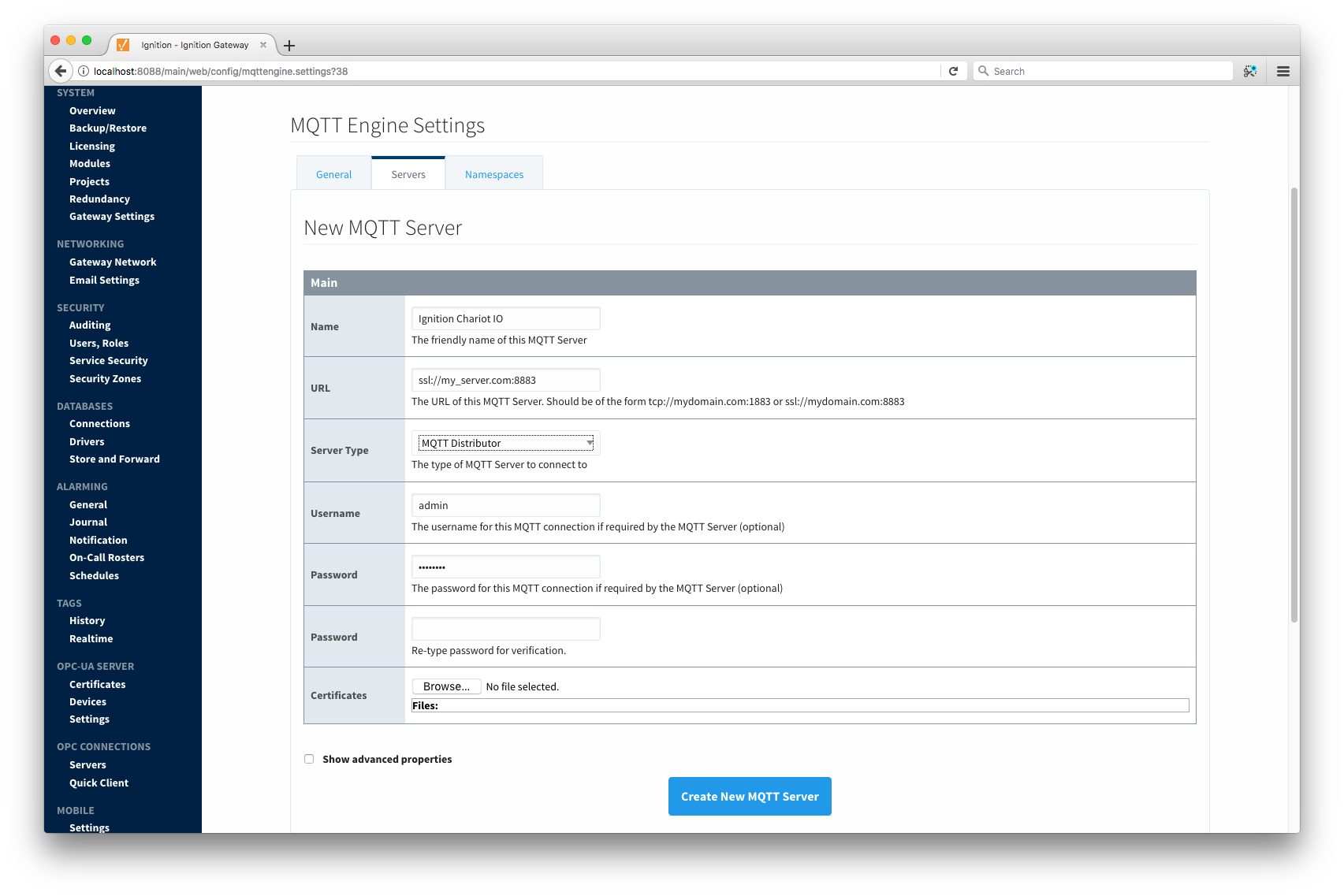
Using the Certificate to Secure Communication with MQTT Engine or MQTT Transmission:
In MQTT Engine or Transmission, there may be a need to specify the TLS components for the client configuration. In the case of using certificates signed by a trusted CA that do not require an internediate cert don't need any special configuration other changing the form of the URL. The form should be as follows:
An example is here:
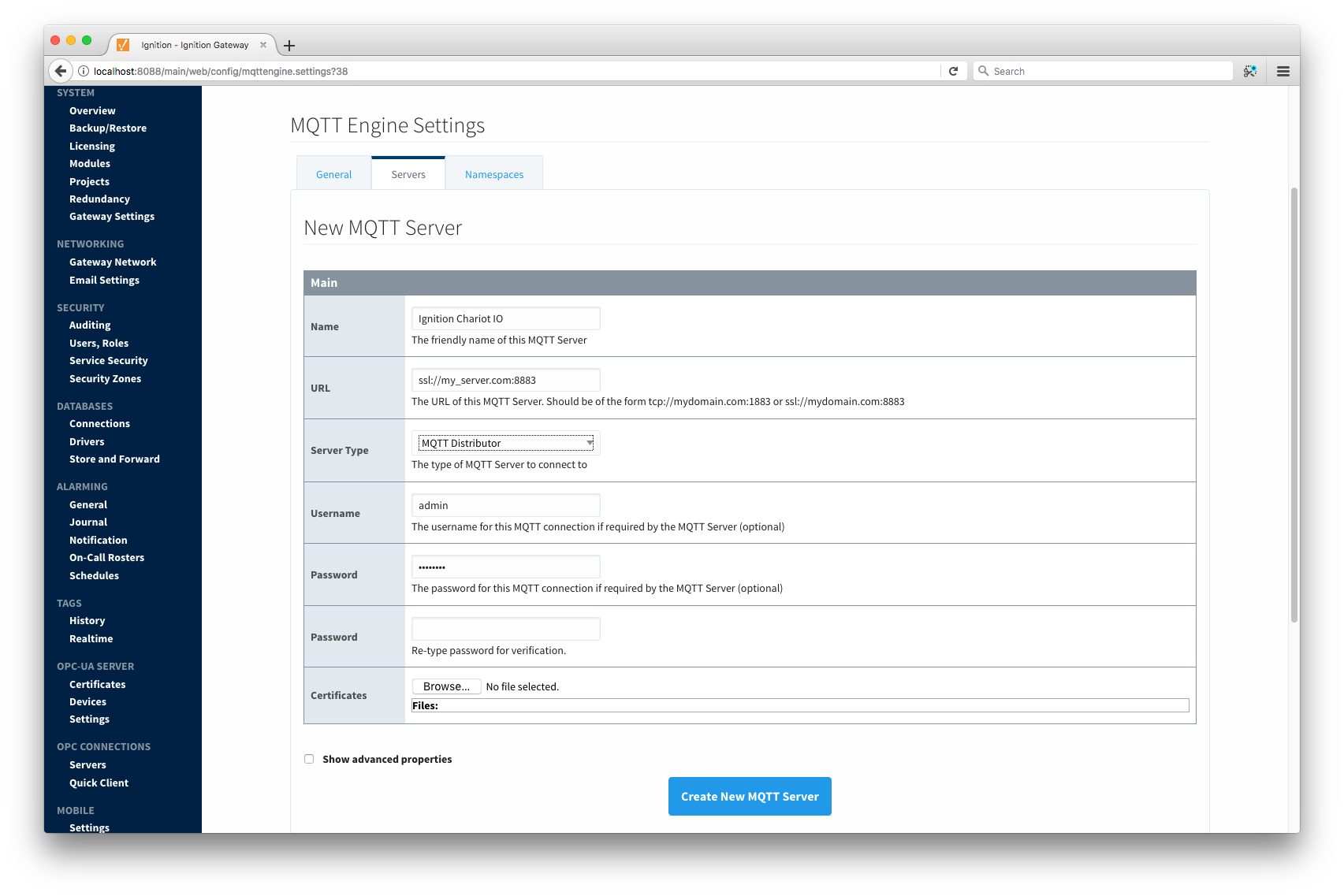 Image Added
Image Added
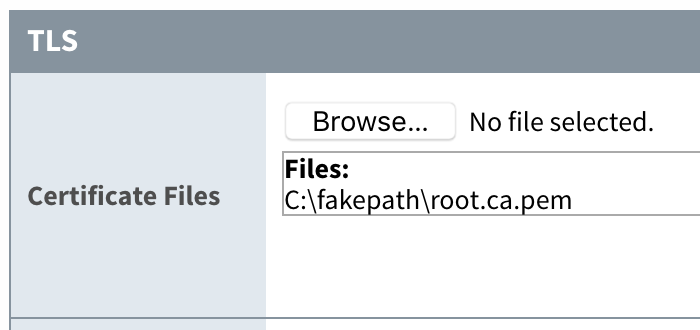
If the trusted CA you purchased your certificate from requires an intermediate certificate or if you created a self signed certificate, you will need to specify the CA certificate chain in the configuration. If you received your certificate from a trusted CA and they require an intermediate certificate, it will be provided by the CA. If you followed the tutorial above for a self-signed certificate and also created an intermediate CA, it will be the file called 'ca-chain.cert.pem'. If you simply created a CA without an intermediate cert, it will be the public CA certificate. Once you've identified the CA certificate chain based on these descriptions, copy it to a file called 'root.ca.pem' on your development system. Note this filename change is important and required. Upload the file via the configuration as shown here by clicking Save Changes:
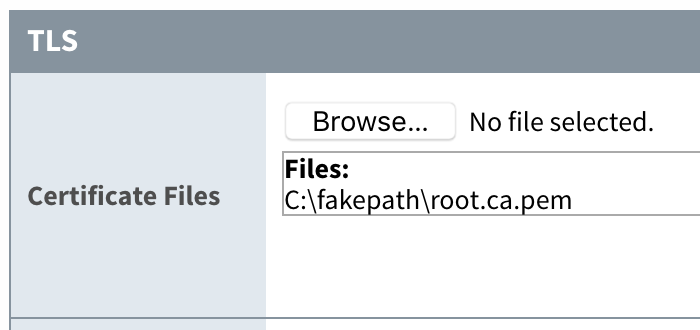 Image Added
Image Added
Once the settings are saved, the MQTT client associated with MQTT Engine or MQTT Transmission will connect using TLS.
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()